By
Imran Hanif, CMgr, FCMI, FIML, MIPSA
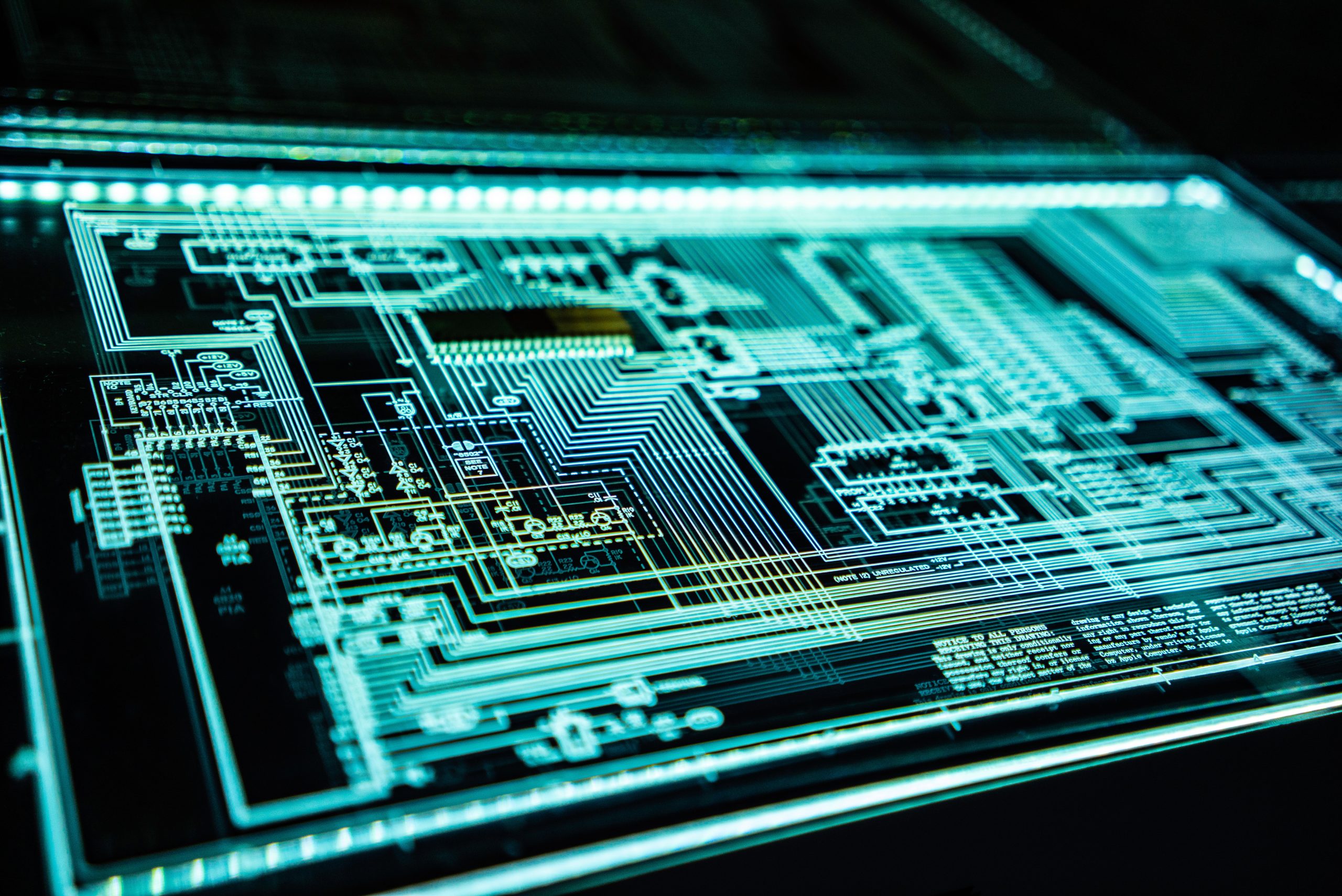
Cyber security is the practice of protecting our electronic infrastructure and computer networks from any threat that could compromise their integrity, availability or confidentiality. Cyber security threats are constantly evolving and becoming more sophisticated, posing significant challenges for individuals, organizations and governments.
In this blog post, we will explore some of the main cyber security threats and challenges that we face in today’s world, and provide some tips on how to prevent or mitigate them.
Advanced Persistent Threats (APTs)
APTs are stealthy and long-term attacks that aim to infiltrate a target’s network and exfiltrate sensitive data or cause damage. APTs often use multiple techniques, such as phishing, malware, zero-day exploits and supply chain compromise, to bypass security defences and remain undetected for months or years. APTs can target any sector or industry, but are especially prevalent in critical infrastructure, government, defence and finance.
To prevent or mitigate APTs, organizations need to adopt a proactive and comprehensive approach to cyber security, including:
- Conducting regular risk assessments and vulnerability scans
- Implementing strong authentication and encryption mechanisms
- Applying patches and updates promptly
- Monitoring network activity and detecting anomalies
- Segmenting networks and isolating critical assets
- Educating employees on cyber security best practices
- Developing incident response and recovery plans
Evolution of Ransomware
Ransomware is a type of malware that encrypts the victim’s data or systems and demands a ransom for their decryption. Ransomware attacks have become more frequent and destructive in recent years, affecting various sectors such as healthcare, education, transportation and energy. Ransomware attackers often use social engineering, phishing or exploit kits to infect their targets, and sometimes threaten to leak or sell the stolen data if the ransom is not paid.
To prevent or mitigate ransomware attacks, organizations need to:
- Implement robust backup and restore procedures
- Avoid opening suspicious attachments or links
- Use antivirus software and firewalls
- Disable unnecessary services and ports
- Enable file extensions and hidden files
- Report any ransomware incidents to law enforcement
IoT Threats
The Internet of Things (IoT) refers to the network of devices that can connect to the internet and communicate with each other. IoT devices can include anything from smart watches and cameras to cars and refrigerators. IoT devices can offer many benefits, such as convenience, efficiency and innovation, but they also pose significant cyber security risks. IoT devices are often poorly secured, lack updates and patches, have default or weak passwords, and collect large amounts of personal data. IoT devices can be compromised by hackers to launch distributed denial-of-service (DDoS) attacks, spy on users, steal data or cause physical harm.
To prevent or mitigate IoT threats, users need to:
- Choose reputable manufacturers and vendors
- Change default passwords and use strong passwords
- Update firmware and software regularly
- Disable unnecessary features and services
- Use encryption and VPNs when connecting to public Wi-Fi
- Review privacy settings and permissions
Cloud Security
Cloud computing is the delivery of computing services over the internet, such as storage, servers, databases, software and analytics. Cloud computing can offer many advantages, such as scalability, flexibility, cost-efficiency and innovation, but it also introduces new cyber security challenges. Cloud security involves protecting the data and applications that are stored or accessed in the cloud from unauthorized access, modification or deletion. Cloud security depends on the shared responsibility model between the cloud service provider (CSP) and the cloud customer. The CSP is responsible for securing the cloud infrastructure and platform, while the customer is responsible for securing the data and applications they use in the cloud.
To prevent or mitigate cloud security issues, customers need to:
- Understand their roles and responsibilities in the cloud
- Choose a trustworthy CSP that complies with relevant standards and regulations
- Encrypt data in transit and at rest
- Use multifactor authentication and access control policies
- Monitor cloud activity and audit logs
- Implement backup and disaster recovery plans
Attacks on Cryptocurrencies and Block chain Technologies
Cryptocurrencies are digital currencies that use cryptography to secure transactions and control the creation of new units. Block chain is a distributed ledger technology that records transactions in a secure, transparent and immutable way. Cryptocurrencies and block chain technologies can offer many benefits, such as decentralization, anonymity, efficiency and innovation, but they also face cyber security threats. Cryptocurrencies and block chain technologies can be attacked by hackers who aim to steal funds, manipulate transactions, and disrupt networks or compromise privacy. Some of the common attack vectors include phishing, malware, social engineering, 51% attacks, double-spending attacks and smart contract vulnerabilities.
To prevent or mitigate attacks on cryptocurrencies and block chain technologies, users need to:
- Use reputable platforms and wallets
- Protect their private keys and passwords
- Verify transactions before confirming them
- Avoid public Wi-Fi networks
- Update software regularly
- Follow security news and alerts
Attacks Enhanced by AI and Machine Learning
Artificial intelligence (AI) is the simulation of human intelligence processes by machines, such as learning, reasoning and self-correction. Machine learning (ML) is a subset of AI that enables machines to learn from data without explicit programming. AI and ML can offer many benefits for cyber security, such as improving detection accuracy, automating tasks and enhancing user experience. However, AI and ML can also be used by hackers to enhance their attacks or evade detection. Some of the potential applications of AI/ML for malicious purposes include generating fake content (such as deep fakes), creating adaptive malware (such as polymorphic malware), launching intelligent DDoS attacks (such as botnets), exploiting vulnerabilities (such as zero-day exploits) or bypassing authentication systems (such as biometrics).
To prevent or mitigate attacks enhanced by AI/ML, organizations need to:
- Adopt a holistic approach to cyber security that considers both human factors (such as awareness) and technical factors (such as defense)
- Leverage AI/ML for cyber defense purposes (such as threat intelligence)
- Incorporate adversarial testing into their AI/ML systems (such as adding noise)
- Implement ethical principles into their AI/ML development (such as transparency)